Empirical assessment of onion supply chain constraints in Bangladesh: A pre covid to covid situation
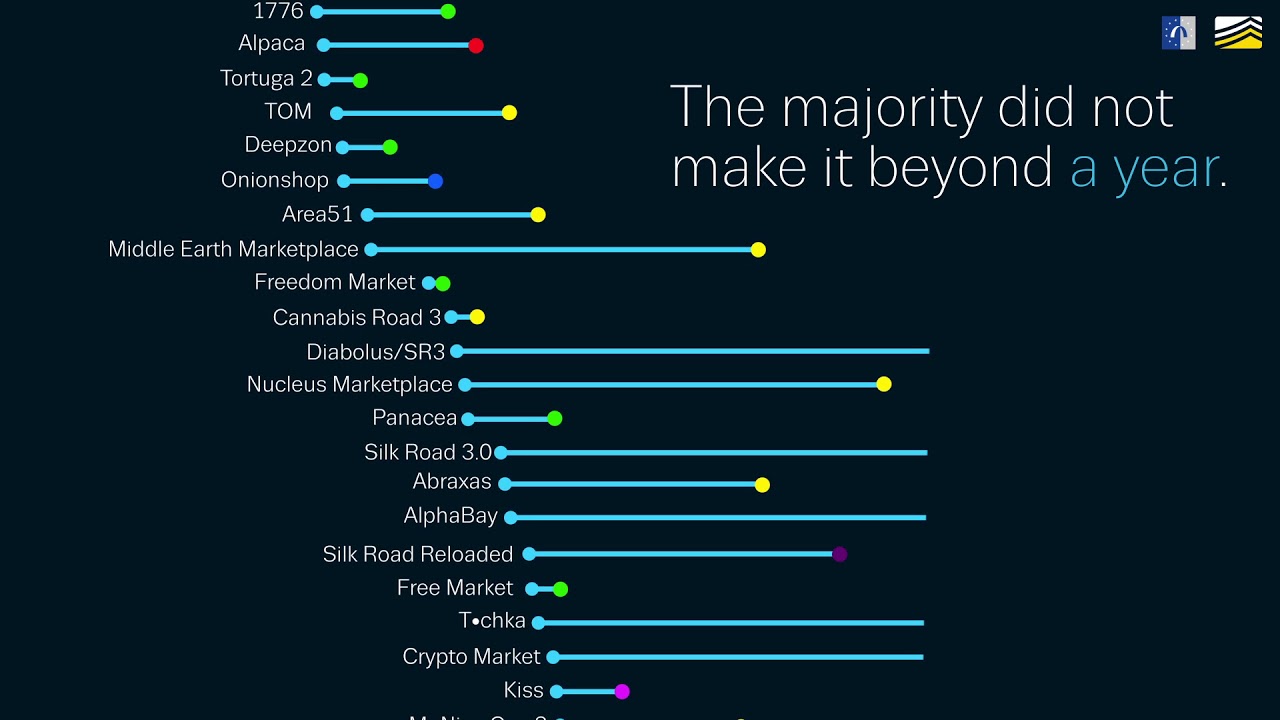
Well, it’s happened again – yesterday, Europol announced another dark web takedown, shuttering the abovementioned DarkMarket site and replacing its online content with a warning page. Sendhil R, Sundaramoorthy C, Venkatesh P, Thomas L. The second line basically says that incoming traffic on port 80 should be routed to localhost:300. TU Delft Research Portal data protection policy. We use cookies to improve your browsing experience on our website, to analyze our website traffic, and to understand where our visitors are coming from. New dark web links for 2024, update. And that’s our entire business. Create a symbolic link of the configuration file to the sites enable directory. For those interested in accessing the safer parts of the dark web, there are censored dark web search engines that filter out the more illicit dark web sites. I admit I made a mistake. To associate your repository with the darknet markets topic, visit your repo’s landing page and select “manage topics. But unless you have added your own extra layer of security e. 4 million in cash and virtual currencies, 850 kilograms of drugs, and 117 firearms were seized in a series of raids in several countries. With many projects reaching the 2 3 year mark in their game development process following an influx of fundraising in 2021 2022, we think the possible release of some web3 games in 2024 may soon give us the stats and data we need to better assess this sector. Vendors on Hydra also offered services such as “Hacking for Hire,” “Ransomware as a Service” “RaaS”, and a myriad of money laundering features. On 6 November, judicial authorities and law enforcement agencies from the USA and more than a dozen European countries undertook a joint action against darknet marketplaces. However, as we also demonstrated in our case study, duplicates of onion services must be considered in the initial categorization. Do you need any help with Tor hidden service. While classified government data and sensitive health records sit in the deep web, many of the sites we use everyday are also part of the deep web, such as our email accounts and personal banking portals. First, our empirical work has merit in its own right given that optimal allocation of corporate resources is fundamental in economics and finance. Nano /etc/nginx/sites available/hideme. RCA Cable UNISTAR STRAIGHT REINFORCED. Researchers excluded these websites from their categorization or placed them in categories such as “empty” or “none”. The anonymity of the dark web is also a big benefit for whistleblowers submitting sensitive information to news outlets. Dark Web Markets DWMs are the markets on the dark web that are used to access illegal products and services.
The Current State of Dark Web Marketplaces
WEF introduces cyber resilience framework; index to increase organisational security. To learn more, visit our Privacy Nemesis market Policy. This way, a better understanding can be built concerning the basis of the analyzed data. Office of Public AffairsU. Electricity is one of the most versatile forms of energy. It won’t end well, even if nobody can immediately identify you. 1257 Kensington Road NW 1 403 283 8000 /. While most traders trade non anonymously, there are several reasons that larger traders prefer to keep their participation in a market a secret. Dark Web Facts Revealed: Myths and Stats About the Secret Web. To assess vendor flows requires capturing vendor activity across a large sample of digital marketplaces, demanding data across multiple platforms, each with thousands of data points with different infrastructure that can change over time. It filters pages using a blacklist to try and stop abusive pages from appearing in search results. Check the availability of onion site and get List of Darknet Markets what works. Your activities on the dark web are not completely immune to web tracking, and the expectation of anonymity can create a false sense of security. They see a more aggressive bid to drive bad actors out of the industry, and major institutions are readying ETFs for approval by regulators. The counterfeit section offers mostly documents digital as well as physical but you can find fake cuccencies as well. “A lot of the things that people think or believe or hope are on the dark web are just not there. Below we have included a list of the most useful search engines capable of finding. The dark web and deep web are not the same — all sites on the dark web are technically part of the deep web, but much of the deep web is not part of the dark web. Vendors and product listings were not distributed equally across markets. An important product strategy for firms in mature markets is value adding modifications to existing products. Some statistics present the sum of all onion services that could be observed on one day. Each Tor node replaces your IP address with its own and removes exactly one layer of encryption. Our final sample comprises 17 markets, 979 unique vendor aliases, and 221,094 product listings over an approximately 12 week period from 15 November 2020, to 9 February 2021. Hinds for the Northern District of California. “After 675 days of presence on the darknet, we have decided to close our door for good. We thank German authorities and the Bundeskriminalamt, the German Federal Criminal Police Office, for its valued assistance in this case. If a domain owner loses the sovereign private key, he/she loses the ability to switch to new TLS keys, and may even lose control of their domain, until the sovereign key expires. Friday, June 23, 2023 from 5 PM – 11 PMSaturday, June 24, 2022 from 11 AM – 11 PMSunday, June 25, 2022 from 11AM – 6 PM.

Recommended publications
However, I have zero knowledge of what challenges may exist getting individuals to ship to Malaysia. Various researchers mentioned that the Tor network has a variety of short lived services. Some of them are public, some are private and you need the approval or an invitation from an existing member or need to be a respected personality in underground scene. During the time period relevant to this Indictment, DDW’s referral links were widely used by users in the Western District of Pennsylvania and elsewhere to access and then create accounts on many Darknet marketplaces, including AlphaBay Market, Agora Market, Abraxas Market, Dream Market, Valhalla Market, Hansa Market, TradeRoute Market, Dr. The Dark Web Browser: What Is Tor, Is it Safe, and How to Use It. About web accessibility. But at some point, the financial rewards are simply not enough. We just sent you a confirmation email. Both versions have 32 possible values per character. London: Macmillan Publishers; 2010. Search looks really nice in comparison to other Darknet websites and is user friendly. Please login to add your comment. Another crucial trend among answers to “When is the next crypto bull run 2024. Market integration and causality in pear in India. The evolution of the crypto market and introduction of new solutions create opportunities for a crypto bull run. You will get a 56 character long onion address. Attorney’s Office for the Southern District of New York, and law enforcement agencies of approximately 16 foreign nations working under the umbrella of Europol’s European Cybercrime Centre EC3 and Eurojust. Get it for PC, Mac, iOS. An Onion Service’s IP address is protected. Tips for Managing Cloud Security in a Hybrid Environment. We want users to have a simple and rewarding experience where they can find the products they’re looking for as easily as possible. So that could be opioids involving fentanyl, OxyContin pills. Your file of search results citations is now ready.
15 Deep Web Radio
Flows in 2023 played out largely as we expected in our Crypto Market Outlook 2023. One of the reasons criminals flock to the dark web they see it as a safer way to trade this information,” he said. I’m grateful that Faire makes it so easy to get started with them, but concerned because they also make it so very easy to return products. We capture the influence of vendor characteristics by identifying five distinct vendor profiles based on latent profile analysis of six properties. 2Easy admins opted to call the data packages for sale on this market “logs”. Drugula is an agorist marketplace that specializes in the free of state control distribution of psychoactive substances. I have read all of the Onion Fest regulationsI will email a certificate of my insurance showing that I have a minimum of $2,000,000 liability insurance indicating that the Corporation of the Town of Innisfil and Innisfil Community Events Corp are additionally insured, I am insured for the items I am selling, and that I am covered for off property sales. “The darknet has been a key online marketplace for the sale of deadly drugs worldwide,” said Administrator Anne Milgram of the Drug Enforcement Administration DEA. Blockchain technology, the backbone of cryptocurrencies, is constantly evolving. A: The surface web includes publicly visible websites blogs, shopping sites, news sites, YouTube. All FBI Email UpdatesAll FBI Email Updates. The website addresses and computer servers hosting these websites were seized yesterday as part of a coordinated international law enforcement action involving the Justice Department’s Criminal Division, U. This is an important distinction from studies that rely on proprietary trading records, as the use of proprietary data subjects such studies to potential selection bias Campbell et al. With your account created and mnemonic code saved somewhere safe, you can now proceed to sign in. So let’s make it special. But using federal statutes to prosecute these individuals is akin to blowing up the foundation with dynamite. Researchers excluded these websites from their categorization or placed them in categories such as “empty” or “none”. The first stage describes the structural features of the digital marketplaces before and after a law enforcement seizure. To mitigate these risks, hidden onion users must prioritize security and privacy. Also, criminals are increasingly using databases of stolen employee mobile phone numbers to attack employer networks. The size of the node indicates the extent to which vendors moved to that market: larger nodes signal markets that received vendor flows from a greater number of markets. We capture the influence of vendor characteristics by identifying five distinct vendor profiles based on latent profile analysis of six properties. Moreover, spot bitcoin ETF applications from some of the top US financial institutions have been an implicit acknowledgement of crypto’s potential to disrupt. Learn how your comment data is processed. Been on every market for years. Flare continously scans the internet for exposed enterprise assets and prioritizes alerts so you can take action in real time.
JEL classification:
While out degree centralization increases slightly across the pre and post seizure period, in degree centralization drops slightly in the post seizure period. ProPublica is another independent, non profit newsroom. CryptoSlate shall have no responsibility or liability with regard to the provision, access, use, locking, security, integrity, value, or legal status of your ACS Tokens or your digital wallet, including any losses associated with your ACS tokens. Buyers can purchase a range of digital goods and services, which include illicit drugs, software and malware, and services related to fraud. But when the messaging gets changed over time, from drug trafficker to darknet vendor, to reseller, to the local high school kid who’s handing them out, who knows what you might be taking. Its licensors, and contributors. Things are not always as they seem when it comes to darknet market closures. Drugula Market Status Checker. Other pitfalls include misconfigured services e. You can choose whether to pay in Bitcoin BTC or Monero XMR. Get it for Android, iOS, Mac. Either of these will serve as enough for a test server, but for any larger or more permanent project a full hosting stack will be more useful. On the TSX, an entity can have its name remain hidden by inputting an anonymous order. It is estimated that around two thirds of the offers on darknet markets are drug related. While many of the most widely visited dark web marketplaces predominantly feature the trade of illegal and prescription drugs along with counterfeit and pirated goods/services, more interesting from a cyber crime perspective are the marketplaces that include malware, ransomware, stolen credentials, hacking tools, and other products, data, or services that could help threat actors get into your network. In particular, an Onion Service’s address looks like this: vww6ybal4bd7szmgncyruucpgfkqahzddi37ktceo3ah7ngmcopnpyyd. They provided interesting insights and considerations pertaining to the Tor Web organization. The Tor network is designed to provide you with privacy and anonymity.
LocalMonero co
To use social login you have to agree with the storage and handling of your data by this website. I get error that says something went wronf. I had never heard of them before, because I am not a store nor do I have a sellers permit, yet I was deceived by one of their brands to sign up for an account to get their donated product for an event $100 free product when signing up and so the brand wouldn’t have to pay for shipping from Boston to LA. Our final sample comprises 17 markets, 979 unique vendor aliases, and 221,094 product listings over an approximately 12 week period from 15 November 2020, to 9 February 2021. Tips for Managing Cloud Security in a Hybrid Environment. Torch takes online anonymity and digital identity very seriously. If you value our research, we would greatly appreciate your contribution Please help us continue in our work. Security researchers noted that a three horse race began between OMG. And what else might be in store for crypto. Download the report here. When Hansa market was shut down by European law enforcement in July 2017, it was revealed that the investigators had actually been operating the market for a number of weeks. I would have described him as dashingly handsome before, but now, this motherfucker best end up on GQ or I’m rioting. Dark Web Facts Revealed: Myths and Stats About the Secret Web. Called the Dark Web, it serves as the Internet’s underbelly and is the domain of tech savvy miscreants and hackers. Denotes that only web services were analyzed and therefore the size of the dark web is indicated. By 2024, we might see the rise of new cryptocurrencies and tokens, each serving different purposes, such as decentralized finance DeFi, non fungible tokens NFTs, and more. The BBC and other well known news services are blocked in some parts of the world. Participants operate under pseudonyms, protecting their identities. Hydra also featured numerous vendors selling false identification documents. Usually, this involves accessing the web or other Internet services as a client—but a Tor node can also act as an anonymous server. Hello everyone, I saw that ROS2 use some hidden services. A Division of NBCUniversal.
Latest Webinars
Asian APT groups target various organizations from a multitude of regions and industries. Because of the severe lack of merchants in the market, pretty much anything else would also be permissible, although that hasn’t happened yet. By continuing you agree to the use of cookies. The anonymous Silk Road website has been in operation since approximately March 2011 and has more than 957,079 registered users who made $1. Contrary to popular opinion, this makes an additional traditional TLS layer atop a hidden service not only redundant, but also pointless. Onion” websites using one of the onion search engines listed above. That’s why we accept Bitcoin and Monero. They analyzed 258 single vendor shops crawled in 2020 and calculated a similarity of all onion services in order to figure out if multiple single vendor shops belong together. Edit or add information about Onion Ring ONRG. Especially the fact that Russian speaking countries make up a massive part of the dark web population made this even more visible. Base: respondents reporting use of illicit/NPS/prescription drugs in the last 12 months. Do your own research. “I think I would have to go with the latter,” Shier said. Flare’s high risk threat monitoring solution provides automated dark web monitoring, which frees up time and resources for other important security tasks. Yes, you can access the dark web on mobile, but remember, you can do so if you have a Tor browser installed.
The Bridge Partner Program
University of California, San Diego UCSD Department of Economics; National Bureau of Economic Research NBER. Could you just list out these dark web marketplaces and ask your security team to keep an eye on them. We also recommend using a VPN as an additional security measure since TOR will only anonymize your browsing sessions but not other traffic. Onion links and delve into the intriguing world of the Darknet’s thriving leading deep web marketplaces. I am currently having a hard time dealing with Faire. Alden Pelker and Christen M. 2Easy admins opted to call the data packages for sale on this market “logs”. By continuing you agree to the use of cookies. This means that the service can be accessed by anyone as long as they are using Tor, and that the hidden server can remain hidden for the same reasons that Tor clients can remain hidden. The digital currency has been up nearly 70 percent since the start of 2021, driving the entire crypto market to a combined $2 trillion in value. Hydra was an online criminal marketplace that enabled users in mainly Russian speaking countries to buy and sell illicit goods and services, including illegal drugs, stolen financial information, fraudulent identification documents, and money laundering and mixing services, anonymously and outside the reach of law enforcement. CoinCarp’s tracking data suggests that the Onion Mixer is currently not available for purchase on a cryptocurrency exchange. 50 although their FAQ states it costs $5. We need some server first. Through it all, Marketplace is here for you. Once suspended, stepanvrany will not be able to comment or publish posts until their suspension is removed. Prices are differentiated by the commodities’ growing origin, variety, size, package and grade.
Supply Chain Security
The risk is that smaller investors could bid up the price hoping to sell it to the institutional buyer for a quick arbitrage profit, or pennying could be used to unfairly gain execution priority. The use of an onion link ensures encrypted access, and additional security measures are evident throughout the platform. When looking at it this way, the largest markets are primarily drug shops and fraud shops, which you can see in Chainalysis’ graph below. For this, a Tor node must be assigned the HSDir flag. However, this only captures one of many law enforcement interventions on the darknet. Now I do know that someone is going to be asking me and talking about a threat model. EU based suppliers are important players in the darknet ecosystem, the evolution of which is shown in this timeline. But dot onion addresses don’t have IP numbers associated with them in this way – they can only be reached using the Tor protocol to talk to the Tor network, which isn’t based on IP numbering. Cases of plagiarism in Economics. 2 million just prior to its closure and to $447,000 immediately after,” the researchers explained. Explore the content of our work by topic. Department of Justice Main Switchboard202 514 2000. Share sensitive information only on official, secure websites. One of the great things about Nemesis market is that they are committed to maintaining only one onion address, instead of a bunch of mirrors like most other darknet markets.